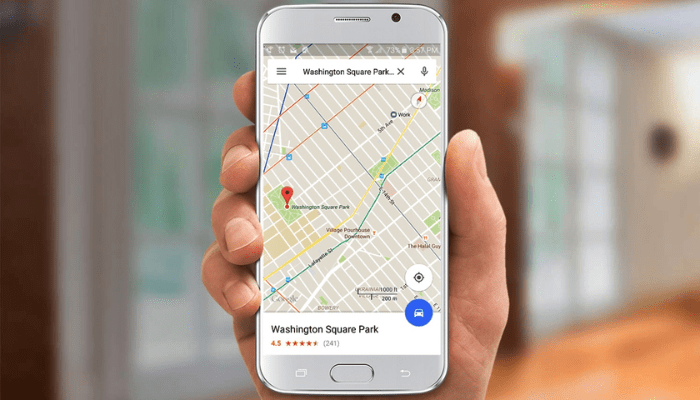
How to locate anyone by cell phone number?
Is it safe to use this tracking mode?
How does the number location mode work?
Location by cell phone number is an increasingly sought after feature, integrating cutting-edge technologies to offer precision and security in tracking mobile devices. This method exploits the potential of modern communication networks and global positioning systems, allowing users to locate devices in real time. In this way, it becomes an essential tool both for personal security and for facilitating connections between people.
To understand how it works, follow this detailed list:
- Signal Triangulation : Uses the cell phone’s proximity to telephone towers to estimate its location.
- GPS (Global Positioning System) : Captures signals from satellites to accurately determine the device’s location.
- Wi-Fi and Bluetooth : Some methods include analyzing nearby Wi-Fi networks and Bluetooth devices for more accurate localization indoors.
- Tracking Applications and Services : Require the device to be associated with a specific account, allowing location through dedicated applications or features built into the operating system.
- Consent : Fundamental to the entire process, the device user’s consent is mandatory to respect privacy and comply with applicable laws.
By adopting these technologies and following the correct procedures, locating a cell phone by number becomes a safe and effective process, reflecting advances in contemporary mobile technology.